Navigation
Install the app
How to install the app on iOS
Follow along with the video below to see how to install our site as a web app on your home screen.
Note: This feature may not be available in some browsers.
More options
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
Windows 7 is now on Technet
- Thread starter TechieSooner
- Start date
BinarySynapse
[H]F Junkie
- Joined
- Feb 6, 2006
- Messages
- 15,103
Keep telling yourself that
There were once people that proclaimed how secure WEP was too, and we all know how that turned out.
Locking down a network is a completely different concept than verifying the contents of a file.
MD5 and SHA1 use two different algorithms to verify that the contents match the provided hashes. It's damn near impossible to fake one alone, but to change the file in a way that fakes both algorithms? yeah not gonna happen.
SO let's see.
You have an MD5 hash, and SHA1 hash and a file size.
You want to add a malicious program to the image, which changes the output hash (which mind you is done on users end, not yours, so there's no way you can exploit the hash checks), but doing that changes the hash. So you have to figure out a way to add bits to the image that'll produce the same hashed as the original two, but since the algorithms are different, each bit changed or added affects the computations differently. Then you have to figure out how to do all of this while retaining the same file size, so you remove some help files, or images, whatever... well that changes the hashes yet again...
DeaconFrost
[H]F Junkie
- Joined
- Sep 6, 2007
- Messages
- 11,588
Glad I took off work today!
LstBrunnenG
Supreme [H]ardness
- Joined
- Jun 3, 2003
- Messages
- 6,676
I don't see where Technet shows the MD5...?Locking down a network is a completely different concept than verifying the contents of a file.
MD5 and SHA1 use two different algorithms to verify that the contents match the provided hashes. It's damn near impossible to fake one alone, but to change the file in a way that fakes both algorithms? yeah not gonna happen.
soulesschild
Supreme [H]ardness
- Joined
- Feb 18, 2007
- Messages
- 6,176
50kb...wooo?
50kb...wooo?
Do I hear 25KB?
BinarySynapse
[H]F Junkie
- Joined
- Feb 6, 2006
- Messages
- 15,103
I don't see where Technet shows the MD5...?
seems that they did provide them someplace else though. maybe I'm wrong. Even still, you have SHA1 and a filesize. Still quite a hill to climb just to spread a cheap little exploit.
TechieSooner
Supreme [H]ardness
- Joined
- Nov 7, 2007
- Messages
- 7,601
Locking down a network is a completely different concept than verifying the contents of a file.
MD5 and SHA1 use two different algorithms to verify that the contents match the provided hashes. It's damn near impossible to fake one alone, but to change the file in a way that fakes both algorithms? yeah not gonna happen.
Yada yada yada...
If you feel the need to go that in-depth to assure yourself of how perfect the hashes are, be my guess.
I, for one, won't.
http://www.win.tue.nl/hashclash/SoftIntCodeSign/
http://www.schneier.com/blog/archives/2005/02/sha1_broken.html
Ummm.... Yea, they're so bulletproof
RangerXML
Supreme [H]ardness
- Joined
- Apr 16, 2006
- Messages
- 6,405
Anyone confirm yet that the CD key work with the leaked RTM from over a week ago?
BinarySynapse
[H]F Junkie
- Joined
- Feb 6, 2006
- Messages
- 15,103
Yada yada yada...
If you feel the need to go that in-depth to assure yourself of how perfect the hashes are, be my guess.
I, for one, won't.
http://www.win.tue.nl/hashclash/SoftIntCodeSign/
http://www.schneier.com/blog/archives/2005/02/sha1_broken.html
Ummm.... Yea, they're so bulletproof
Yeah, first one's bust since they had to change both files to match MD5. Now if they added code to the second program only, to match the first, It'd be a better example. but they still have to deal with the file's size.
Reading the second one now.
Anyone confirm yet that the CD key work with the leaked RTM from over a week ago?
Yes, works fine. No matter what TechieSooner comes up with, you can't fake an MD5, SHA-1 AND a CRC hash all at the same time.
Low Roller
[H]ard|Gawd
- Joined
- Jun 24, 2004
- Messages
- 1,024
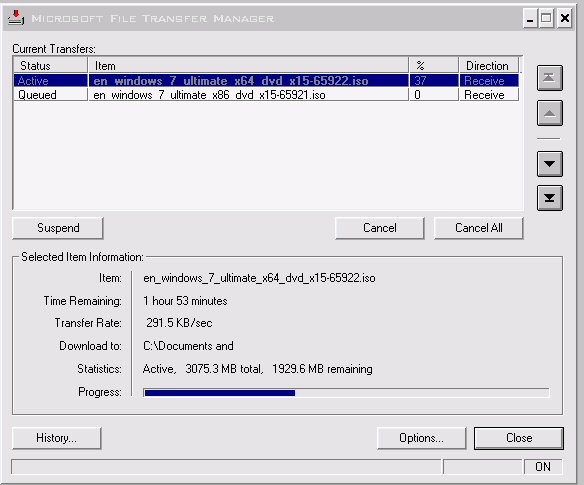
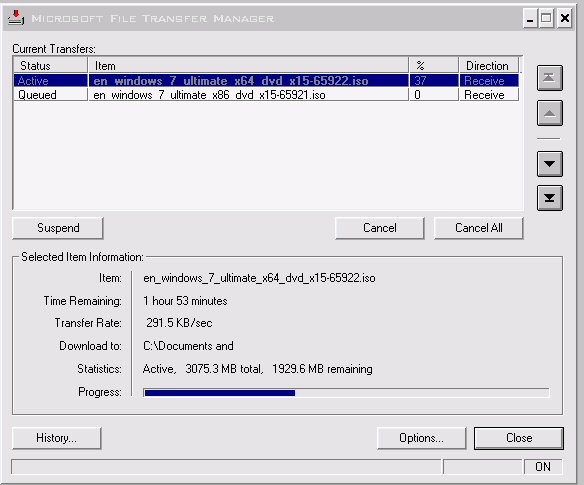
smokin' along here at ~120KB/sec 
TechieSooner
Supreme [H]ardness
- Joined
- Nov 7, 2007
- Messages
- 7,601
Doesn't matter, the point is that they matched the MD5.Yeah, first one's bust since they had to change both files to match MD5
TechieSooner
Supreme [H]ardness
- Joined
- Nov 7, 2007
- Messages
- 7,601
Yes, works fine. No matter what TechieSooner comes up with, you can't fake an MD5, SHA-1 AND a CRC hash all at the same time.
I'll make a note of that for next year when someone comes out with their method to spoof the hashes... Saying something will never be broken is just fucking ignorant.
It's like downloading a virus on purpose because "It's OK, if this is really VirusX, I have the signatures for it in my AV client."
A bit of common sense goes a long way.
BinarySynapse
[H]F Junkie
- Joined
- Feb 6, 2006
- Messages
- 15,103
Doesn't matter, the point is that they matched the MD5.
by changing both files, the control and the variable. You can't exactly do that with a file located and hashed elsewhere.
Do you not realize how widely relied on these security methods are? Why do you think MS gives them out? SHA was developed by the NSA for christ sake!
IMO its fucking ignorant to think its so easy to fake them and the entire security community would not be in an uproar!
IMO its fucking ignorant to think its so easy to fake them and the entire security community would not be in an uproar!
I'll make a note of that for next year when someone comes out with their method to spoof the hashes... Saying something will never be broken is just fucking ignorant.
It's like downloading a virus on purpose because "It's OK, if this is really VirusX, I have the signatures for it in my AV client."
A bit of common sense goes a long way.
Please leave the computer field
BinarySynapse
[H]F Junkie
- Joined
- Feb 6, 2006
- Messages
- 15,103
I'll make a note of that for next year when someone comes out with their method to spoof the hashes... Saying something will never be broken is just fucking ignorant.
It's like downloading a virus on purpose because "It's OK, if this is really VirusX, I have the signatures for it in my AV client."
A bit of common sense goes a long way.
spoofing requires actively intercepting the hashing program and changing its results. You have a known key provided from a legitimate source (MS), and a program to check the file you downloaded. The only way to fake the hash is to change the file itself is such a way that manages to create a hash that matches the original. a simple 40kb file took 832bytes to BOTH files to accomplish. Don't see it happening with 4.3 billion bytes.
Monkey God
Mangina Full of Sand
- Joined
- May 7, 2007
- Messages
- 6,723
Slow, but downloading, yay!
Menelmarar
Supreme [H]ardness
- Joined
- Feb 15, 2001
- Messages
- 5,472
So where are these HASH and MD5 values published for the layman? I've got my Microcenter $39 pre-order coupon tacked to my noteboard... but obviously no key til Oct 22 =/
I've got two different ISO's from online, both claim to be rtm, final, both have different md5 hashes, eeep. Honestly probably both legit, one is just compiled by user other by MS, but I'd prefer the MS one. I still have to remove the file that makes Ultimate install by default, grrr.
I've got two different ISO's from online, both claim to be rtm, final, both have different md5 hashes, eeep. Honestly probably both legit, one is just compiled by user other by MS, but I'd prefer the MS one. I still have to remove the file that makes Ultimate install by default, grrr.
DeaconFrost
[H]F Junkie
- Joined
- Sep 6, 2007
- Messages
- 11,588
Can I ask a question/ How gives a flying shit about the hashed and such? Really? If you download it yourself from TechNet....who cares? If you stick to downloading the legit code from the legit source, why bother spending time and effort arguing about it?
So where are these HASH and MD5 values published for the layman? I've got my Microcenter $39 pre-order coupon tacked to my noteboard... but obviously no key til Oct 22 =/
I've got two different ISO's from online, both claim to be rtm, final, both have different md5 hashes, eeep. Honestly probably both legit, one is just compiled by user other by MS, but I'd prefer the MS one. I still have to remove the file that makes Ultimate install by default, grrr.
Direct from Technet: http://bayimg.com/image/hadobaacb.jpg
AMD T-type
Supreme [H]ardness
- Joined
- Aug 26, 2002
- Messages
- 4,590
So where are these HASH and MD5 values published for the layman? I've got my Microcenter $39 pre-order coupon tacked to my noteboard... but obviously no key til Oct 22 =/
I've got two different ISO's from online, both claim to be rtm, final, both have different md5 hashes, eeep. Honestly probably both legit, one is just compiled by user other by MS, but I'd prefer the MS one. I still have to remove the file that makes Ultimate install by default, grrr.
what version and architect hash do you want?
x64 Ultimate is SHA1: 326327CC2FF9F05379F5058C41BE6BC5E004BAA7
Can I ask a question/ How gives a flying shit about the hashed and such? Really? If you download it yourself from TechNet....who cares? If you stick to downloading the legit code from the legit source, why bother spending time and effort arguing about it?
We are all in front of our computers.. why not?
And its aggravating seeing the ignorance about such ingrained security measures.
LstBrunnenG
Supreme [H]ardness
- Joined
- Jun 3, 2003
- Messages
- 6,676
Does anyone have a complete download from Technet or MSDN?
RangerXML
Supreme [H]ardness
- Joined
- Apr 16, 2006
- Messages
- 6,405
Does anyone have a complete download from Technet or MSDN?
the only complete downloads anyone has are the leaked versions, everyone else is going to be a bit still.
leezard
Supreme [H]ardness
- Joined
- Aug 24, 2004
- Messages
- 4,949
maybe after the rush dies down I'll put up a FS thread to get myself another technet sub (work wont pay for it  ) Already have pro on pre order but wouldnt bitch to much about getting ult just for the hell of ot
) Already have pro on pre order but wouldnt bitch to much about getting ult just for the hell of ot
the only complete downloads anyone has are the leaked copy, everyone else is going to be a bit still.
Fixed.
PureBooYah
2[H]4U
- Joined
- Aug 26, 2002
- Messages
- 3,363
I'll make a note of that for next year when someone comes out with their method to spoof the hashes... Saying something will never be broken is just fucking ignorant.
It's like downloading a virus on purpose because "It's OK, if this is really VirusX, I have the signatures for it in my AV client."
A bit of common sense goes a long way.
Even if someone ends up breaking it in the future, right now it's not broken. And your analogy is horrible.
Can I ask a question/ How gives a flying shit about the hashed and such? Really? If you download it yourself from TechNet....who cares? If you stick to downloading the legit code from the legit source, why bother spending time and effort arguing about it?
Because someone brought up that the legit version has been out for weeks which started the argument of how did they know it was legit which brought up the discussion on hashes.
Menelmarar
Supreme [H]ardness
- Joined
- Feb 15, 2001
- Messages
- 5,472
Beautiful, Thank you!Direct from Technet: http://bayimg.com/image/hadobaacb.jpg
That's the one! I really need Home Premium, but the only ISO's floating around seem to be strictly Ultimate. I just want to make sure I start with a trusted ISO to modify in order to get Home Premium.what version and architect hash do you want?
x64 Ultimate is SHA1: 326327CC2FF9F05379F5058C41BE6BC5E004BAA7
30 day eval + rearm should get me through to Oct 22 =) for real cdkey.
thefordmccord
[H]ard|Gawd
- Joined
- Jun 20, 2001
- Messages
- 1,044
i'm still chugging along just fine. It should be done by the time I get home from work!!!
Here you go bitches:
Ultimate x64:
SHA1: 326327CC2FF9F05379F5058C41BE6BC5E004BAA7 CRC: 1F1257CA
Ultimate x86:
SHA1: 5395DC4B38F7BDB1E005FF414DEEDFDB16DBF610 CRC: C1C20F76
Home Premium x64:
SHA1: 336779EA6B65F63E11A609B4D021439C47AB315B CRC: 56D954E4
Home Premium x86:
SHA1: CC9D8220B2179E784D85BF1EA98D2EE2190D534F CRC: 5DF6DBA0
Pro x64:
SHA1: 50127304441A793EE51B3F501289F6599A559E9F CRC: 502C42C1
Pro x86:
SHA1: 697FA06554502FB21D30275273B25747299C020D CRC: 578725D1
Ultimate x64:
SHA1: 326327CC2FF9F05379F5058C41BE6BC5E004BAA7 CRC: 1F1257CA
Ultimate x86:
SHA1: 5395DC4B38F7BDB1E005FF414DEEDFDB16DBF610 CRC: C1C20F76
Home Premium x64:
SHA1: 336779EA6B65F63E11A609B4D021439C47AB315B CRC: 56D954E4
Home Premium x86:
SHA1: CC9D8220B2179E784D85BF1EA98D2EE2190D534F CRC: 5DF6DBA0
Pro x64:
SHA1: 50127304441A793EE51B3F501289F6599A559E9F CRC: 502C42C1
Pro x86:
SHA1: 697FA06554502FB21D30275273B25747299C020D CRC: 578725D1
LstBrunnenG
Supreme [H]ardness
- Joined
- Jun 3, 2003
- Messages
- 6,676
Look, there are known exploits for both MD5 and SHA1. It is highly unlikely, but possible that the ISO has been compromised. It would just take a cryptological genius to do it.
AMD T-type
Supreme [H]ardness
- Joined
- Aug 26, 2002
- Messages
- 4,590
Beautiful, Thank you!
That's the one! I really need Home Premium, but the only ISO's floating around seem to be strictly Ultimate. I just want to make sure I start with a trusted ISO to modify in order to get Home Premium.
30 day eval + rearm should get me through to Oct 22 =) for real cdkey.
http://www.mydigitallife.info/2009/...ll-from-single-edition-dvd-disc-media-or-iso/
BinarySynapse
[H]F Junkie
- Joined
- Feb 6, 2006
- Messages
- 15,103
Look, there are known exploits for both MD5 and SHA1. It is highly unlikely, but possible that the ISO has been compromised. It would just take a cryptological genius to do it.
possible, yes. But it took 832 bytes specifically constructed to modify two tiny files to get the MD5 hashes to match. But I bet if you took the SHA1 hashes of those modified files, they wouldn't match.
So dealing with a DVD sized file and two publicly known hashes, and a known file size, how the hell is anyone going to add a piece of malware, figure out the exact sequence of bytes that'll reproduce the original hashes (not create matching hashes for two modified files) for BOTH algorithms and keep the files sizes the same down to the byte?
edit: TechieSooner, perhaps you should read your entire source link before going on your rampage against hashes:
It is important to note that the hash value shared by the two different files is a result of the collision construction process. We cannot target a given hash value, and produce a (meaningful) input bit string hashing to that given value. In cryptographic terms: our attack is an attack on collision resistance, not on preimage or second preimage resistance. This implies that both colliding files have to be specially prepared by the attacker, before they are published on a download site or presented for signing by a code signing scheme. Existing files with a known hash that have not been prepared in this way are not vulnerable.
Last edited:
LstBrunnenG
Supreme [H]ardness
- Joined
- Jun 3, 2003
- Messages
- 6,676
Solving problems like this is what math super-geniuses live for.possible, yes. But it took 832 bytes specifically constructed to modify two tiny files to get the MD5 hashes to match. But I bet if you took the SHA1 hashes of those modified files, they wouldn't match.
So dealing with a DVD sized file and two publicly known hashes, and a known file size, how the hell is anyone going to add a piece of malware, figure out the exact sequence of bytes that'll reproduce the original hashes (not create matching hashes for two modified files) for BOTH algorithms and keep the files sizes the same down to the byte?
Problem is, if such a person had figured out a method of solving the problem, hacking into Microsoft and changing whatever they wanted would probably be trivial to them
![[H]ard|Forum](/styles/hardforum/xenforo/logo_dark.png)